The Enterprise Agent Harness.
Nightshift gives agent operators the choice for where compute, storage, data, and models live.
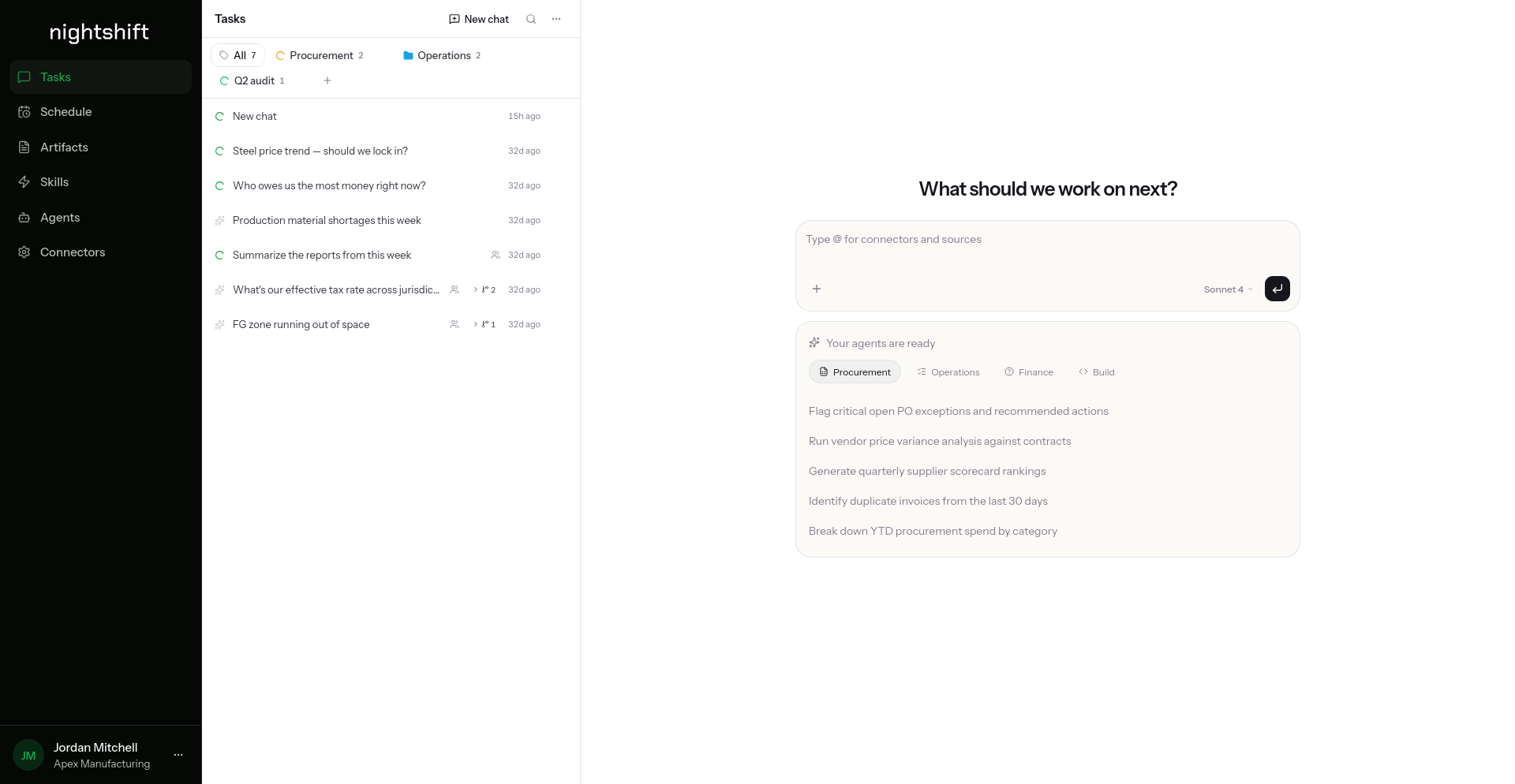
Chat your team already knows.
Feature parity with ChatGPT or Claude. Open Nightshift, start a conversation, and agents work end to end on your infrastructure.
- Plain-English prompts that kick off multi-step agent runs
- Real artifacts inline: dashboards, reports, code, alerts
- One-shot or on any recurring schedule
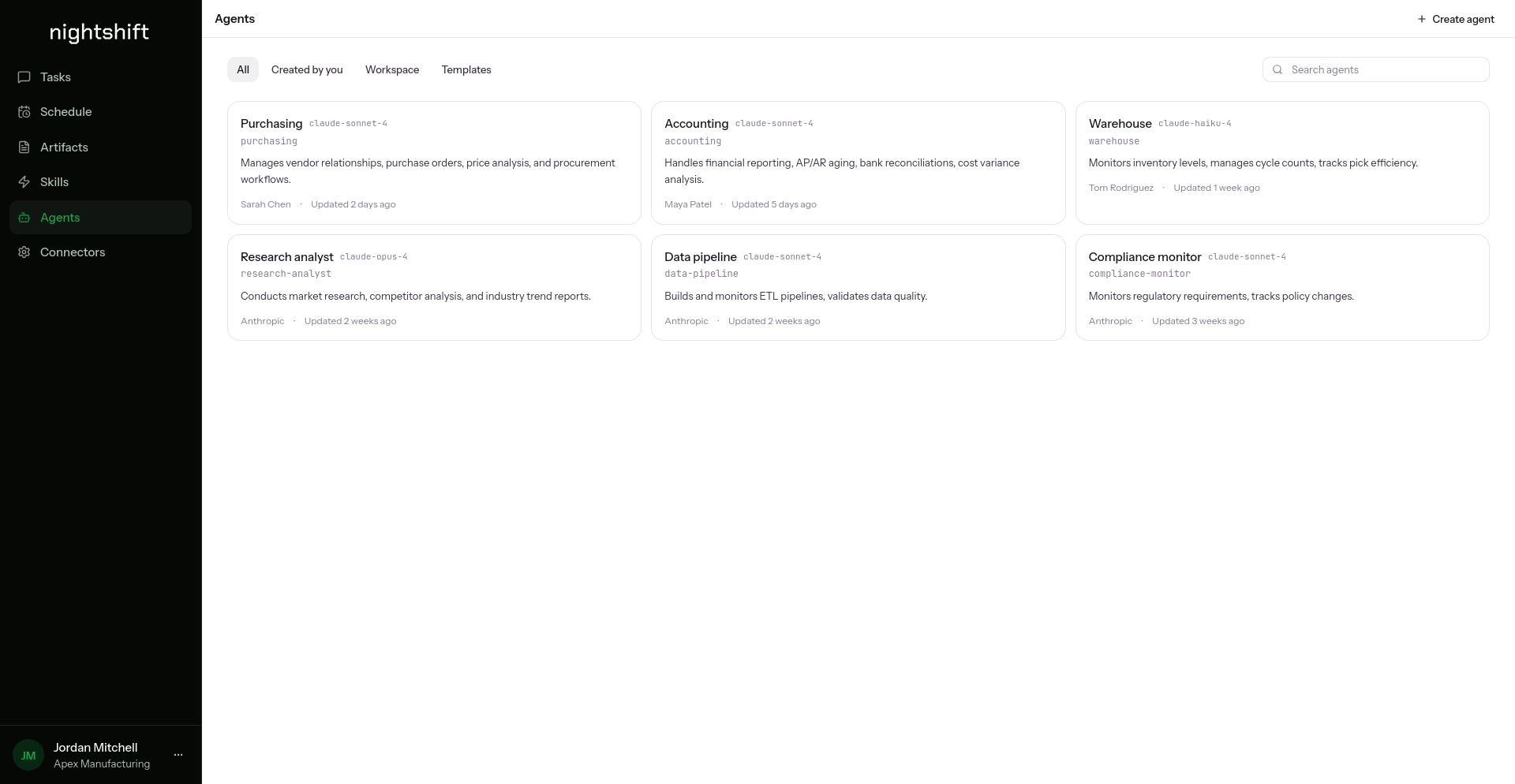
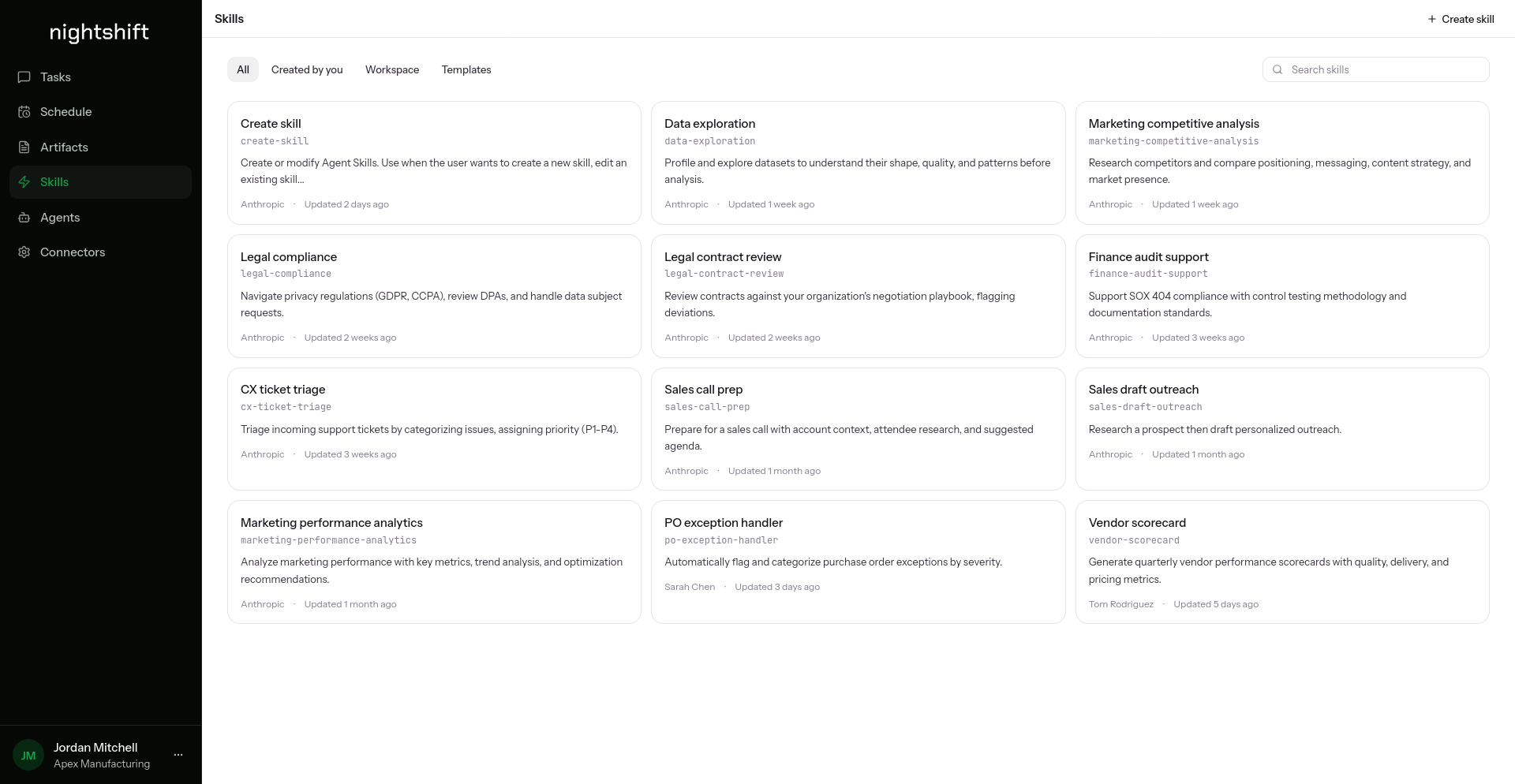
Agents and skills, made easy
Build an agent for every job: Purchasing, Accounting, a Compliance monitor. Each carries its own prompt and scope. Layer in skills as reusable playbooks your team writes once and agents apply on every run.
- Skills are markdown specs your team reads, reviews, and versions
- Apply skills globally or scope them to a single agent
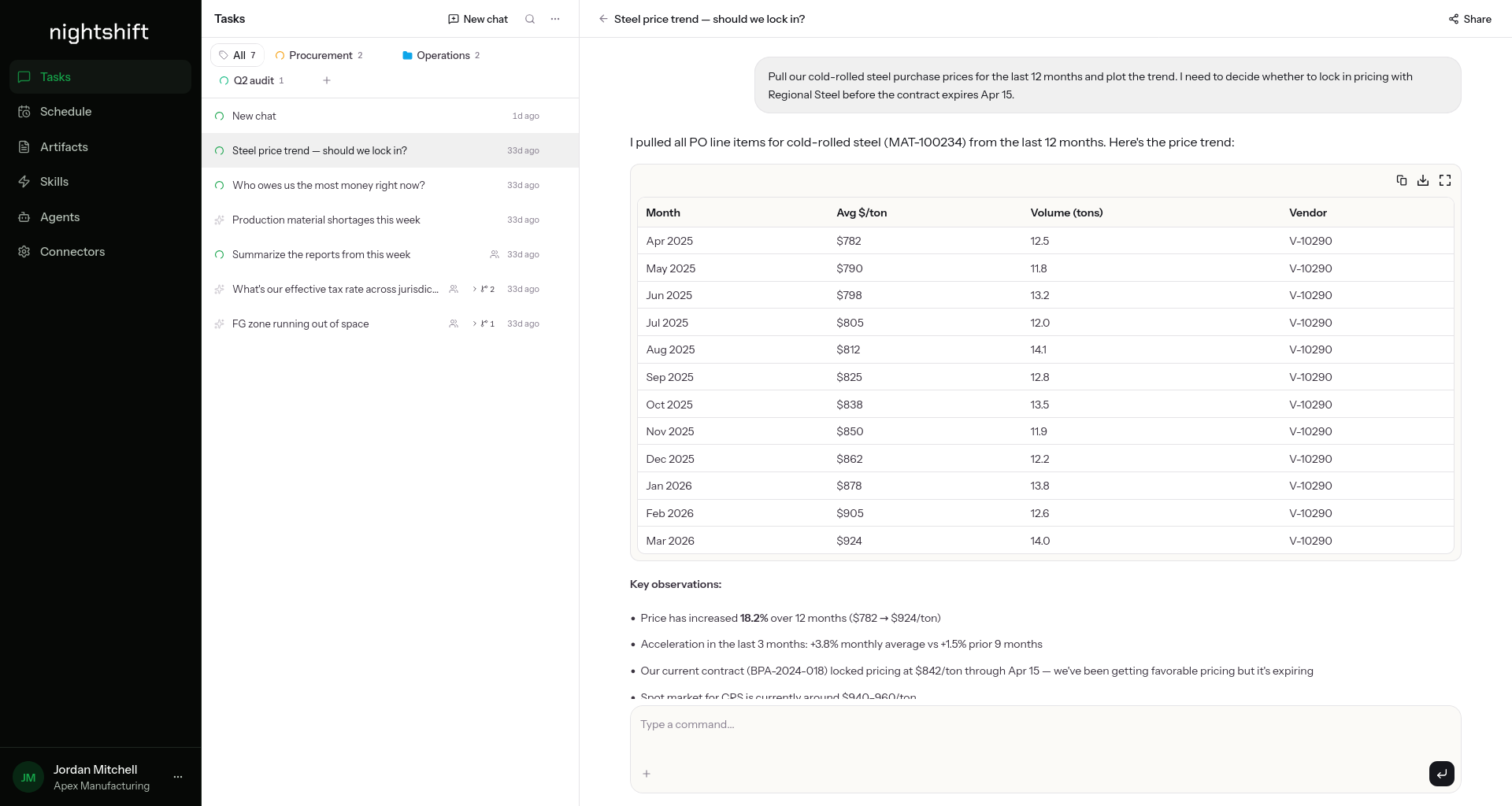
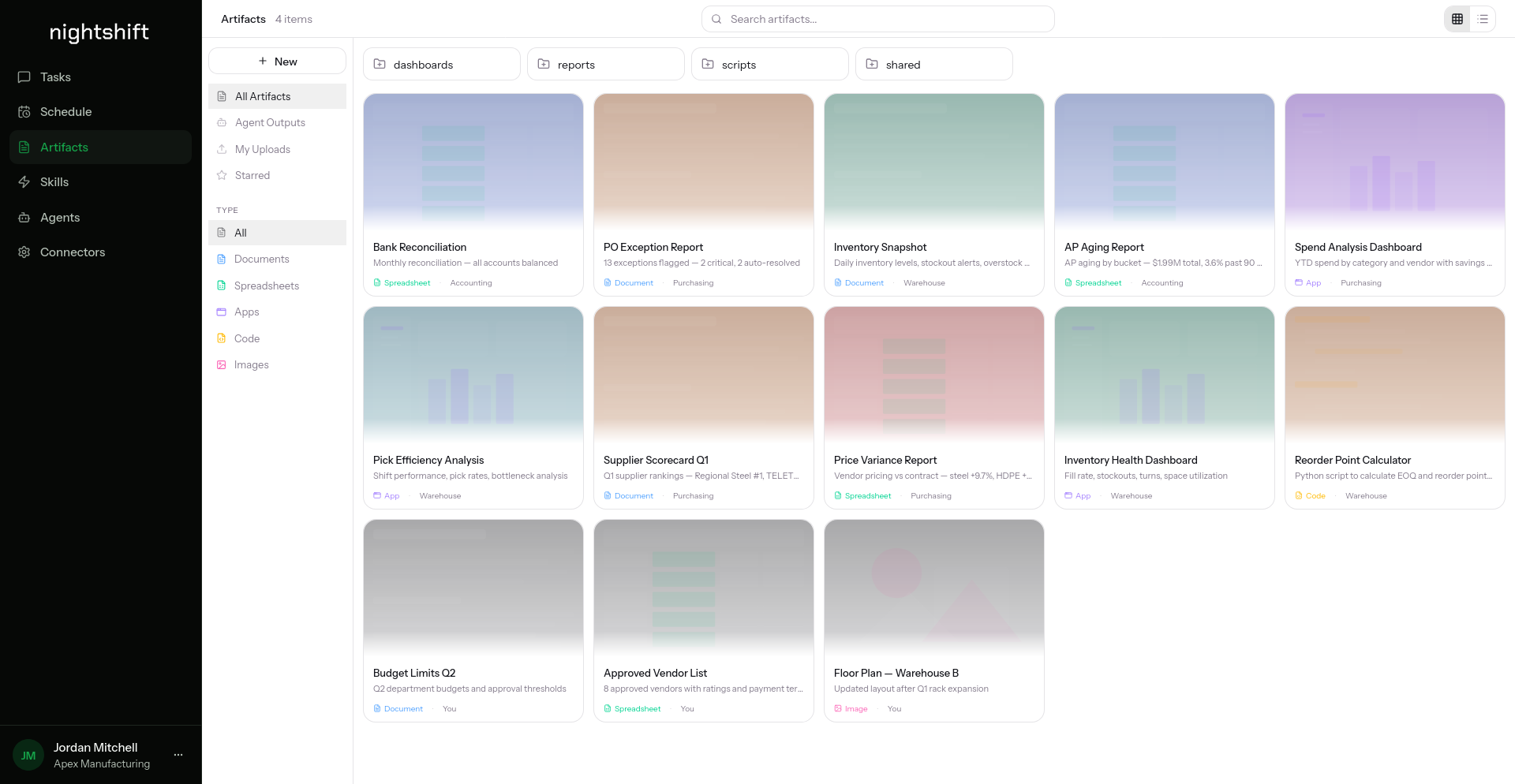
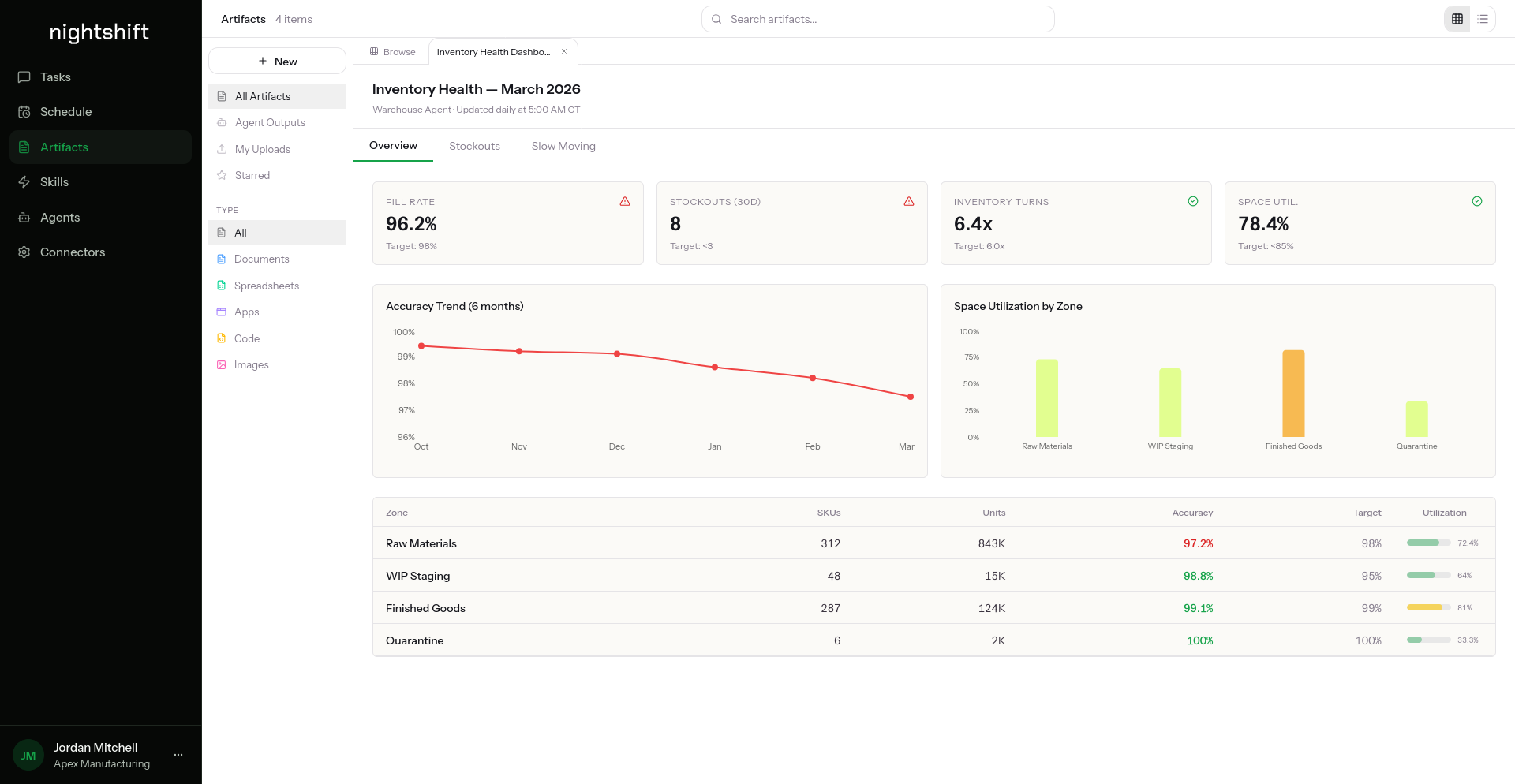
Real work, not just chat
Dashboards, reports, spreadsheets, code, apps. Every artifact an agent produces is browsable, shareable, and traceable back to the run that made it.
- Native types: Documents, Spreadsheets, Apps, Code, Images
- Pin to dashboards, share with your team, or keep private
- Every artifact links back to the run, the agent, and the prompt
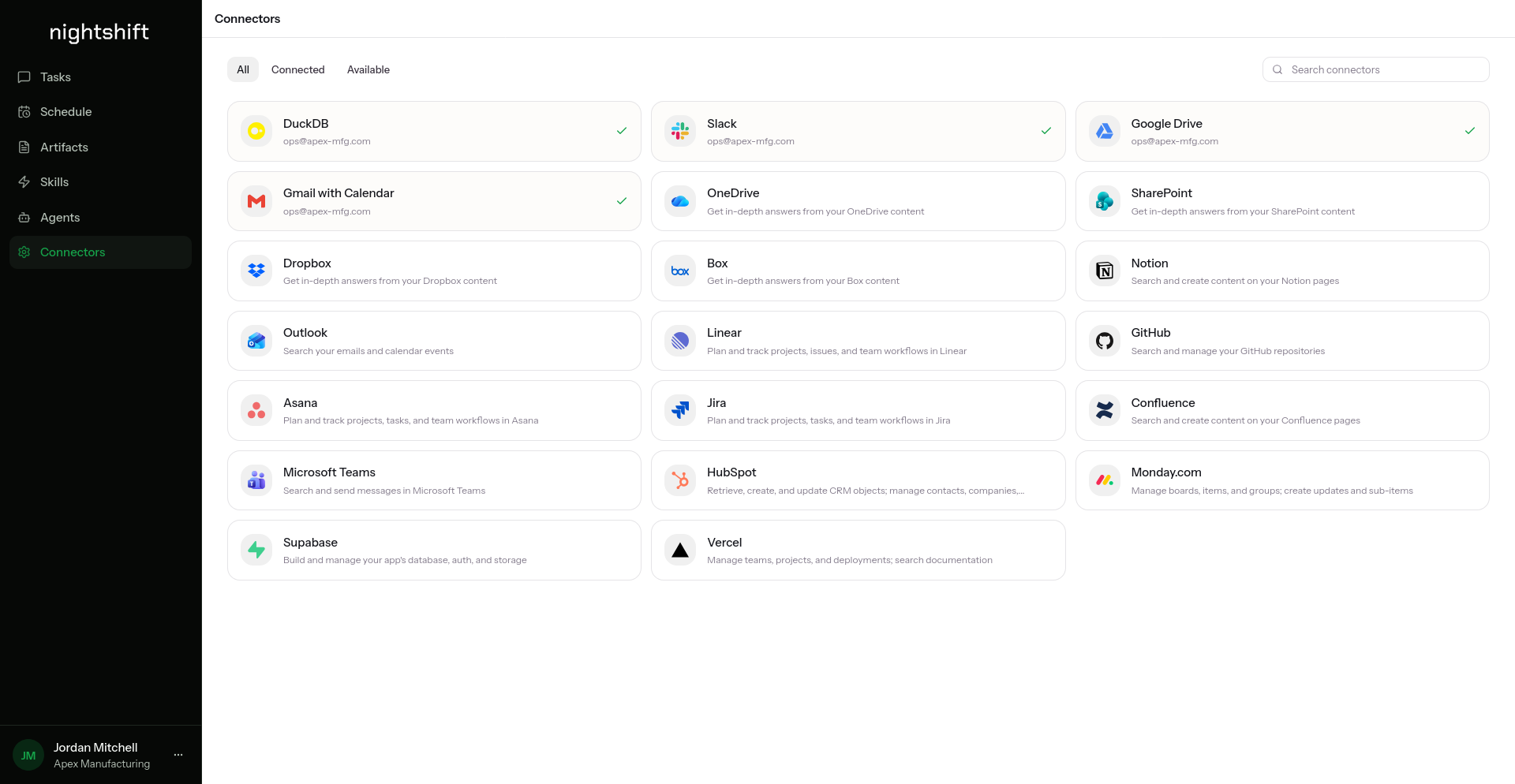
Plug into the tools you already use
A growing library of first-party connectors into the tools your team lives in. We ship new ones every release, and the integration framework is open so you or the community can add your own.
- OAuth or service-account auth: your IdP, your scopes
- Read and write: agents reply in chat, open PRs, update tickets, query warehouses
- Scoped per agent, audited per run, revocable any time
Why Nightshift?
Enterprise-Ready
Built for the controls enterprise security teams expect: hardened defaults, IDP-backed SSO, and an architecture that scales with your org.
Agent Agnostic
Run any agent SDK (Claude, OpenAI, LangGraph, or your own) on the same runtime without lock-in.
Easy to Deploy and Manage
One Helm chart for the full stack. Same chart deploys to a local cluster, your production cluster, on-premise, or fully air-gapped.
Multi-Tenant Support
Strong tenant isolation for teams, business units, or customers — namespaces, identities, and policies scoped per tenant.
Feature-Rich
UI feature parity with the chat products your team already uses, so adoption is one conversation, not a rewrite.
Sovereign
Your compute, your data, your models. Deploy Nightshift on infrastructure you control — cloud, on-premise, or fully air-gapped.
See how Nightshift works across use cases.
Watch agents do real work in the product, then explore how Nightshift adapts to the workflows, connectors, and systems each use case actually runs.
Use Case · Industrial Operations
Procurement, distribution, and the factory floor.
Agents that read and write your ERP, WMS, and MES. They take exceptions off your buyers’ desks, expedite the right pallets, and keep the line moving.
See the use case
Use Case · Coworking
The agentic backbone for flex workspace operators.
Agents for your community managers connected to the tools you already run. Agents for your members in the channels they already use.
See the use case
Latest from the community
AI Should Meet You Where You Are
Why we built Nightshift to adapt to your infrastructure instead of asking your infrastructure to adapt to it.
The Wrong Question About AI Cost
What does AI cost? Wrong question. The right one is what it costs to keep doing the work the way you do it now while a competitor instruments theirs.
Shipping Real Apps with Harness Engineering
Dogfooding Nightshift by running Claude Code inside a chicklet to migrate production infrastructure, fix a live ETL bug, and ship a full-stack feature. Harness engineering at the platform level.
Put agents to work.
See Nightshift run real work end to end on your stack. Book a walkthrough with our team.
